CYBERSECURITY & LAW
Security verification, including pen testing
Protect your organization through regular security assessments. Our experienced security experts help you evaluate IT systems and critical business functions.
In our fast-paced and quickly changing world, high demands are placed on the continuous monitoring of companies’ cybersecurity. These requirements originate not only internally, but equally or even more so from customers, partners, regulatory authorities, standards, and legislation.
It’s often beneficial to bring in an independent third party that can perform objective analyses that take all aspects into account. Our experienced security experts help you verify the organization’s IT/OT system and critical business functions. We identify your specific needs and perform tailored assessments and tests. Our experts will perform both manual and automated test cases. In this way the assessment/test focuses on what is relevant and critical for your business. The result will give you a clear picture of your current security posture and a solid basis for any necessary actions. Reporting includes both a written report and a presentation of the results.
How we can help
Our offerings
Security assessment including penetration testing and security tests
Security Assessments are conducted manually and complemented with automated tests when it is suitable.
- Web applications and APIs
- Mobile applications
- Networks
- Cloud
- Infrastructure
- IoT
- LLM
Red Team exercises
A red team exercise is a realistic and comprehensive security test in which experts act as real attackers to uncover and exploit weaknesses in your organization. By exposing your systems and processes to realistic attacks, you can detect risks before they are exploited, strengthen your defenses, and make sure that your business is protected against future threats. This gives you peace of mind, reduces vulnerabilities, and saves both time and money in the long run.
Meet requirements and ensure compliance
Do you need to conduct technical testing to meet DORA requirements – or stay ahead of other regulations such as NIS2? Our program for digital operative resilience provides you with the threat modelling and technical verification your organization needs.
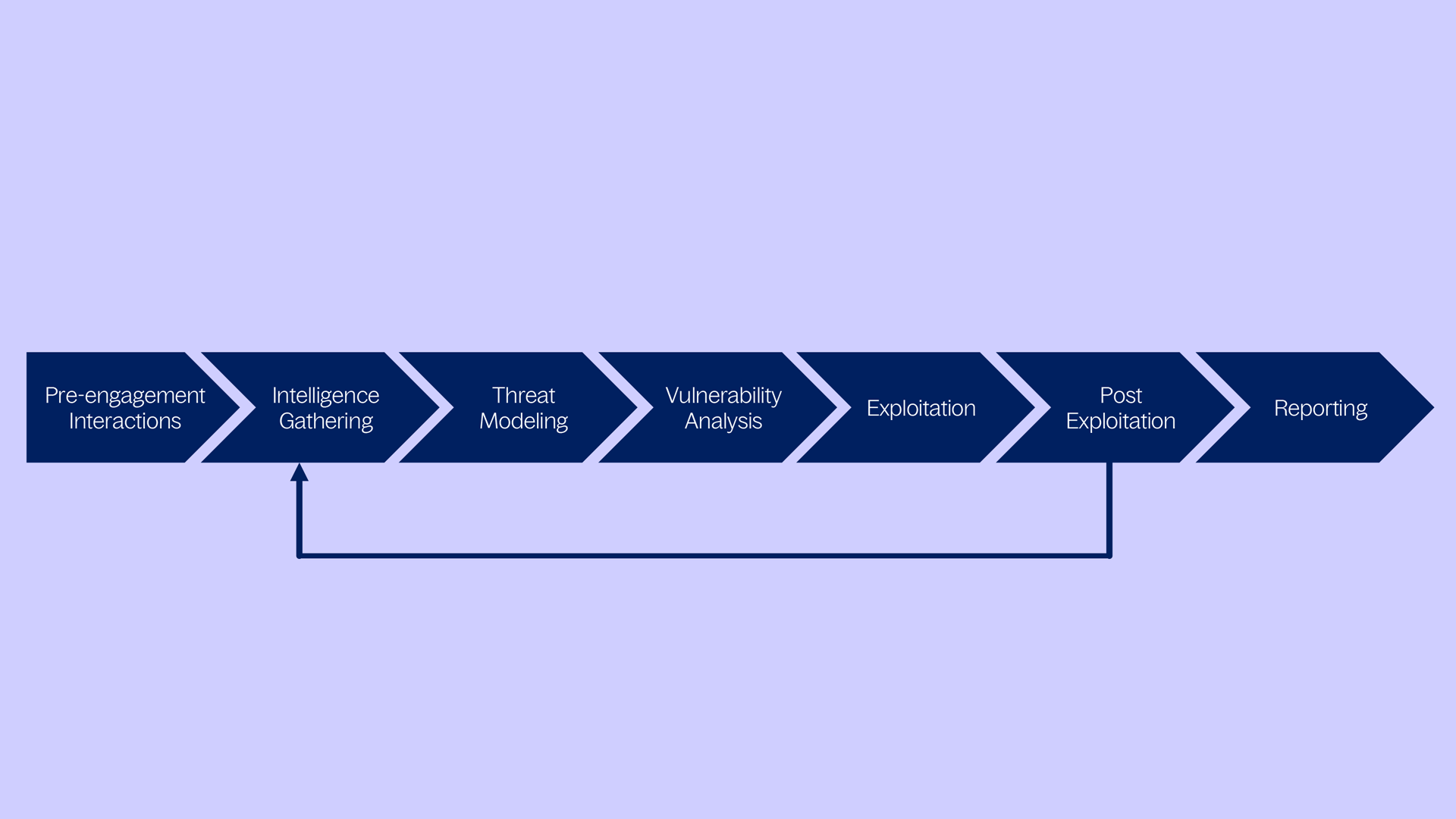
Methodology
Regardless of the scope of the penetration test, the results provide valuable insight into the security risks of the tested systems.
Knowit applies a proprietary methodology for penetration testing based on PTES (Penetration Testing Execution Standard). By following this methodology, we ensure clarity in the scope, execution, and expected results.
Contact us
Do you want to know more? Welcome to contact us for further information.

Pernilla Sander
Sales